| View previous topic :: View next topic |
| Author |
Message |
syst3mboot
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 06 Mar 2019
Posts: 6
|
 Posted: Wed Mar 06, 2019 11:54 am Post subject: Cheat Engine showing different Module address Posted: Wed Mar 06, 2019 11:54 am Post subject: Cheat Engine showing different Module address |
 |
|
Hey guys,
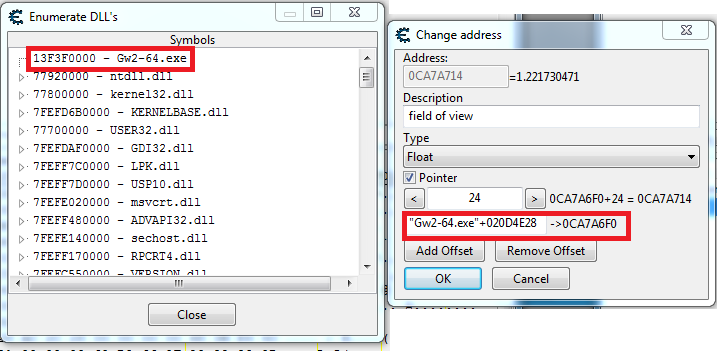
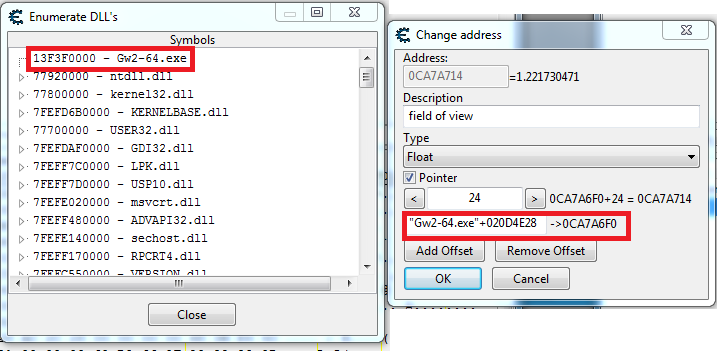
I'm having a problem with cheat engine showing a different module address in the pointer than in Memory Viewer > View > Enumerate DLL's and Symbols.
In memory viewer I have the base address as 13F3F0000 and in the pointer info its 0CA7A6F0 - 020D4E28 = A9A58C8.
I also made a quick C++ program and tried both addresses as the base module and A9A58C8 is the correct one. However when I try to obtain the module base address through C++ I get the same one as Memory Viewer (3F3F0000).
Anyone experienced this and can shed some light into my problem.
| Description: |
|
| Filesize: |
47.17 KB |
| Viewed: |
2734 Time(s) |
|
|
|
| Back to top |
|
 |
OldCheatEngineUser
Whateven rank
 Reputation: 20 Reputation: 20
Joined: 01 Feb 2016
Posts: 1587
|
 Posted: Wed Mar 06, 2019 12:44 pm Post subject: Posted: Wed Mar 06, 2019 12:44 pm Post subject: |
 |
|
no, it doesnt work that way.
your process is 64-bit, so you need to read 8 bytes instead of 4.
- 13F3F0000 is the image_base (which is Gw2-64.exe)
- Gw2-64.exe+020D4E28 is 13F3F0000 + 020D4E28 = 1414C4E28
- value of [1414C4E28] is 0CA7A6F0
- [0CA7A6F0]+24 = 0CA7A714
- [0CA7A714] = float 1.22
so in order to get it programmatically:
- get image base address
- add offset 020D4E28 to it
- then read that address
- add offset 24 to the read address (the address should be in the buffer you passed to ReadProcessMemory)
- when 24 is added, read again but this time read 4 bytes and convert to float
_________________
About Me;
I Use CE Since Version 1.X, And Still Learning How To Use It Well!
Jul 26, 2020
| STN wrote: | | i am a sweetheart. |
|
|
| Back to top |
|
 |
syst3mboot
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 06 Mar 2019
Posts: 6
|
 Posted: Wed Mar 06, 2019 1:24 pm Post subject: Posted: Wed Mar 06, 2019 1:24 pm Post subject: |
 |
|
Ooh I see, Thank you!
Edit: Disregard below, I now realize that DWORD is only 4byte, switched to __int64 and it seems to work better. Ill leave the original post in case someone else has this problem too.
---------------------------------------------------------------------------
Follow up question, I'm writing some code in C++, and on part3
| Quote: | | then read that address |
I get 0x00000000.
This is my code:
| Code: |
DWORD modBase = dwGetModuleBaseAddress(modName); //returns 0x3F860000 - correct
modBase = modBase + 0x020D4E28; //returns 0x41934E28 - correct
//Problem below?
SIZE_T stBytes = 0;
int point1;
ReadProcessMemory(hProc, (LPCVOID)modBase, &point1, 4, &stBytes); //returns 0x00000000 - incorrect
|
I restarted the game so the base address changed, but I cant get the address at base address+offset.
The only difference between what I see here and Cheat Engine is Cheat Engine's module base is 0x13F860000 and mine is 0x3F860000. Though I dont know if that would be the problem.
|
|
| Back to top |
|
 |
OldCheatEngineUser
Whateven rank
 Reputation: 20 Reputation: 20
Joined: 01 Feb 2016
Posts: 1587
|
 Posted: Wed Mar 06, 2019 1:54 pm Post subject: Posted: Wed Mar 06, 2019 1:54 pm Post subject: |
 |
|
| Code: | DWORD modBase = dwGetModuleBaseAddress(modName); //returns 0x3F860000 - correct ///// incorrect, dont use DWORD and make sure the function dont read 4 bytes.
modBase = modBase + 0x020D4E28; //returns 0x41934E28 - correct ///// modBase must 8 bytes long
//Problem below?
SIZE_T stBytes = 0;
int point1;
ReadProcessMemory(hProc, (LPCVOID)modBase, &point1, 4, &stBytes); //returns 0x00000000 - incorrect ///// read 8 bytes |
(read code comments)
note:
int point1;
is signed 32-bit, if address is over 1GB of virtual address space then baaam its overflow.
its fine to use unsigned int, but again if the target address is over 2GB address space then its carry.
it wont hurt if you use DWORD64 or unsigned long long.
_________________
About Me;
I Use CE Since Version 1.X, And Still Learning How To Use It Well!
Jul 26, 2020
| STN wrote: | | i am a sweetheart. |
|
|
| Back to top |
|
 |
syst3mboot
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 06 Mar 2019
Posts: 6
|
 Posted: Wed Mar 06, 2019 2:28 pm Post subject: Posted: Wed Mar 06, 2019 2:28 pm Post subject: |
 |
|
Yah I realized that afterwards. Now the only problem Im having is getting the module base address in 64bits.
| Code: |
DWORD64 dwGetModuleBaseAddress(TCHAR *szModuleName) {
DWORD64 dwModuleBaseAddress = 0;
HANDLE hSnapshot = CreateToolhelp32Snapshot(TH32CS_SNAPMODULE | TH32CS_SNAPMODULE32, pID);
if (hSnapshot != INVALID_HANDLE_VALUE) {
MODULEENTRY32 ModuleEntry32;
ModuleEntry32.dwSize = sizeof(MODULEENTRY32);
if (Module32First(hSnapshot, &ModuleEntry32)) {
do {
if (strcmp(ModuleEntry32.szModule, szModuleName) == 0) {
dwModuleBaseAddress = (DWORD64)ModuleEntry32.modBaseAddr;
break;
}
} while (Module32Next(hSnapshot, &ModuleEntry32));
}
CloseHandle(hSnapshot);
}
return dwModuleBaseAddress;
}
|
Im casting everything to 64bits but
| Code: | | DWORD64 modBase = dwGetModuleBaseAddress(modName); |
Still returns 32bit overflown. 
|
|
| Back to top |
|
 |
OldCheatEngineUser
Whateven rank
 Reputation: 20 Reputation: 20
Joined: 01 Feb 2016
Posts: 1587
|
 Posted: Wed Mar 06, 2019 3:45 pm Post subject: Posted: Wed Mar 06, 2019 3:45 pm Post subject: |
 |
|
| Code: | HANDLE hSnapshot = CreateToolhelp32Snapshot(TH32CS_SNAPMODULE | TH32CS_SNAPMODULE32, pID);
// TH32CS_SNAPMODULE32 will include 32-bit modules and i dont think you need it since your target is 64-bit as well as your project should be. |
_________________
About Me;
I Use CE Since Version 1.X, And Still Learning How To Use It Well!
Jul 26, 2020
| STN wrote: | | i am a sweetheart. |
|
|
| Back to top |
|
 |
syst3mboot
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 06 Mar 2019
Posts: 6
|
 Posted: Wed Mar 06, 2019 4:12 pm Post subject: Posted: Wed Mar 06, 2019 4:12 pm Post subject: |
 |
|
| Thanks for the quick reply, I removed it but still seems to be 32bit :/
|
|
| Back to top |
|
 |
OldCheatEngineUser
Whateven rank
 Reputation: 20 Reputation: 20
Joined: 01 Feb 2016
Posts: 1587
|
 Posted: Wed Mar 06, 2019 4:17 pm Post subject: Posted: Wed Mar 06, 2019 4:17 pm Post subject: |
 |
|
PM is sent, saying i want to see your code. (i will compile it myself and see what happens)
_________________
About Me;
I Use CE Since Version 1.X, And Still Learning How To Use It Well!
Jul 26, 2020
| STN wrote: | | i am a sweetheart. |
|
|
| Back to top |
|
 |
|

 Reputation: 20
Reputation: 20 Reputation: 20
Reputation: 20 Reputation: 20
Reputation: 20 Reputation: 20
Reputation: 20