|
Cheat Engine
The Official Site of Cheat Engine
|
| View previous topic :: View next topic |
| Author |
Message |
Akillibirisi
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 06 Jan 2019
Posts: 8
Location: Turkey
|
 Posted: Sat Apr 06, 2024 2:53 pm Post subject: Find What Writes To Address Weird Results Posted: Sat Apr 06, 2024 2:53 pm Post subject: Find What Writes To Address Weird Results |
 |
|
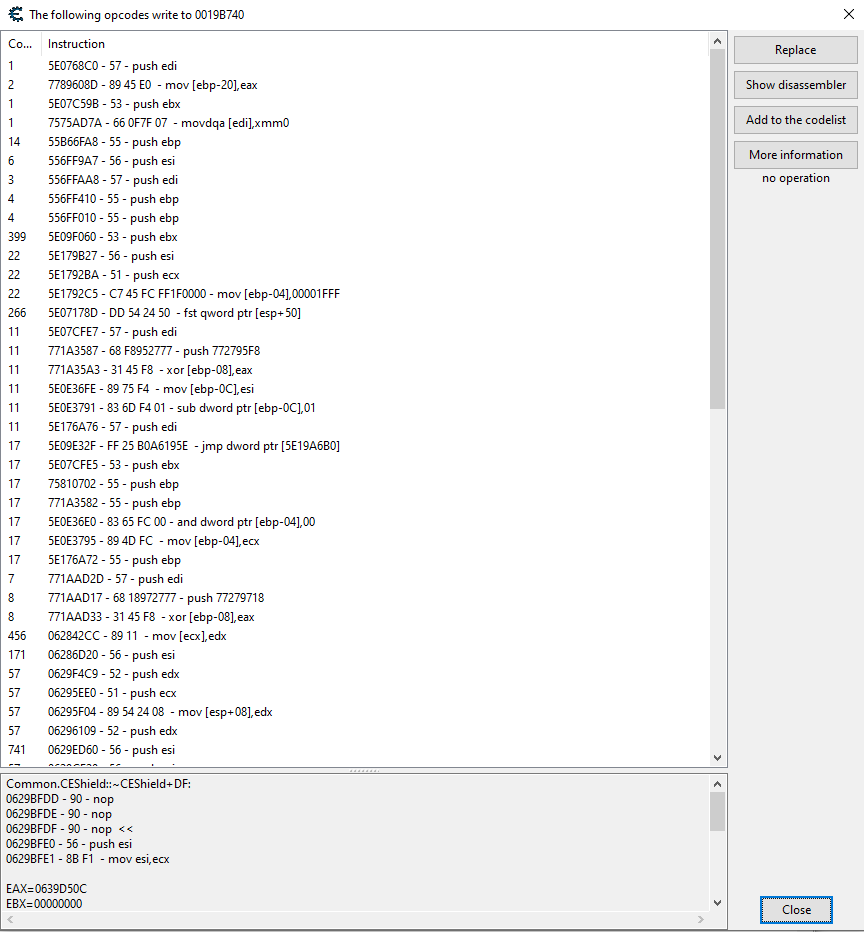
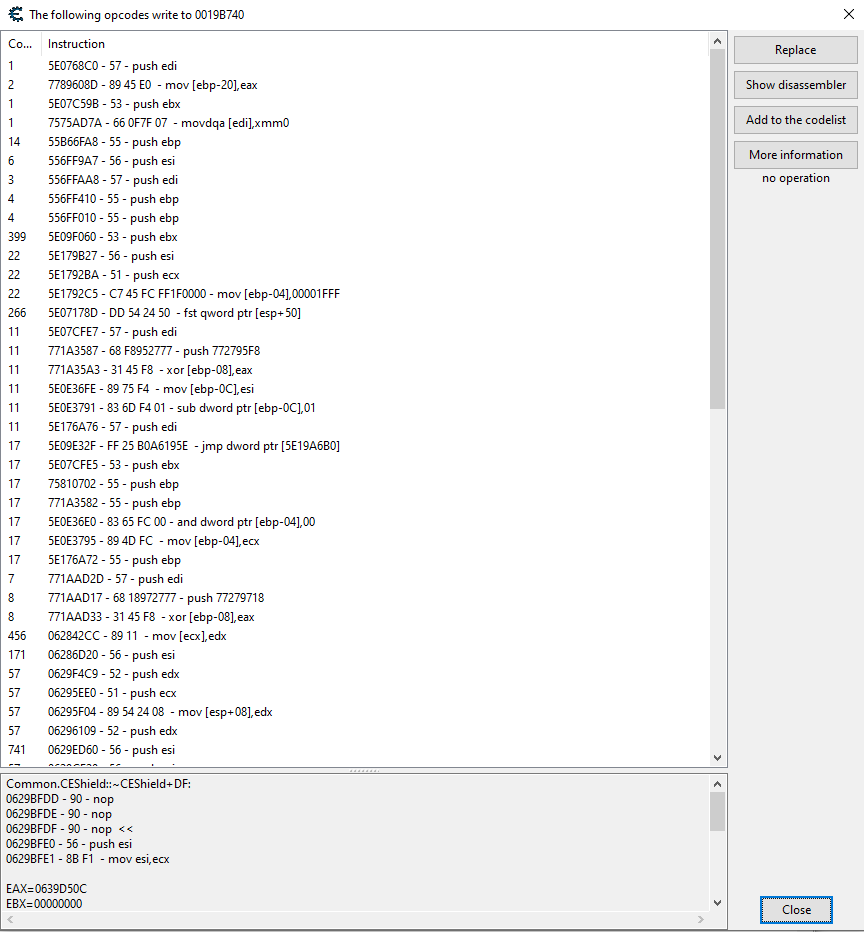
As the image suggests, "Find Out What Writes To Address" returns opcodes like Nop or Push, which I don't see how would be possible without even reference to the address in question. CE version is 7.5
| Description: |
|
| Filesize: |
45.24 KB |
| Viewed: |
915 Time(s) |
|
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 141 Reputation: 141
Joined: 06 Jul 2014
Posts: 4337
|
 Posted: Sat Apr 06, 2024 3:13 pm Post subject: Posted: Sat Apr 06, 2024 3:13 pm Post subject: |
 |
|
That address is in the stack. Instructions like `push` / `pop` access the stack.
As for `nop`, I don't see any in that list (the bottom is probably an instruction you replaced w/ nops afterwards), but it might be some edge case concerning a string operation with a `rep` prefix.
That `jmp` instruction is weird. I'd make the same guess.
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
Akillibirisi
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 06 Jan 2019
Posts: 8
Location: Turkey
|
 Posted: Sat Apr 06, 2024 3:51 pm Post subject: Posted: Sat Apr 06, 2024 3:51 pm Post subject: |
 |
|
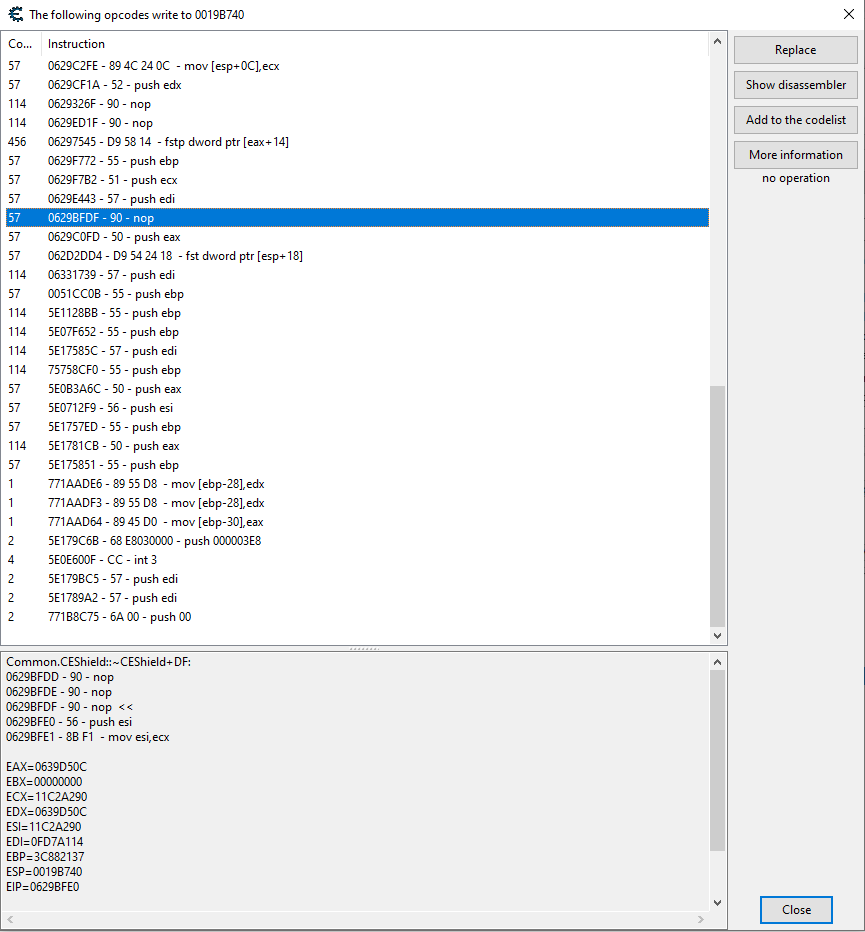
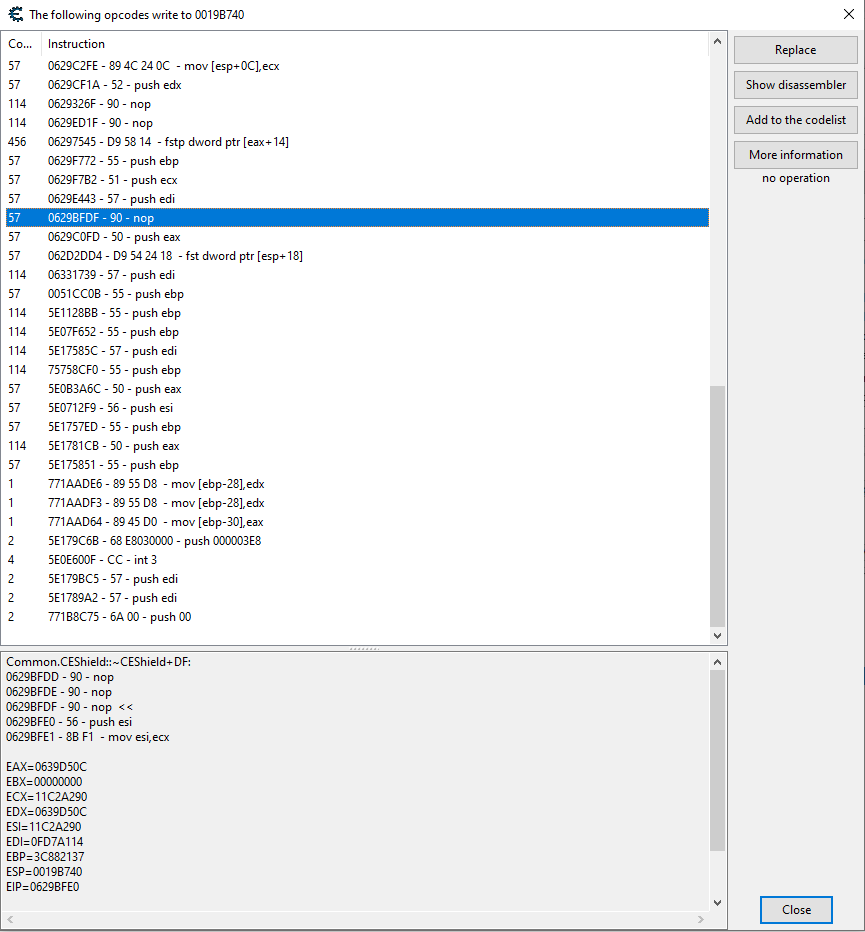
Sorry for the confusion, here's the reupload of the same window scrolled down.
I was expecting that only lines that make direct alterations to the chosen memory location show up in the list. I still can't think of a scenario where stack somehow makes changes to a select memory location.
I'm afraid the original assembly here is completely intact, apart from some friendly value changes here and there. So Nops are the most baffling for me.
Could this "Find Out What Writes" function may be more involved than simply sending the actor by any chance ?
| Description: |
|
| Filesize: |
40.22 KB |
| Viewed: |
902 Time(s) |
|
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 141 Reputation: 141
Joined: 06 Jul 2014
Posts: 4337
|
|
| Back to top |
|
 |
Akillibirisi
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 06 Jan 2019
Posts: 8
Location: Turkey
|
 Posted: Sat Apr 06, 2024 6:02 pm Post subject: Posted: Sat Apr 06, 2024 6:02 pm Post subject: |
 |
|
I mean, instructions like Nop, Call or Push followed by direct register reference, by nature, cannot alter the memory area that is not the stack, to my knowledge.
If my target address is pointed to by [esp] register and instruction "mov [esp],esi" executes, then that's the part I should be seeing, not the part where it is pushed, followed/preceded by nops, called or anything.
push esi will alter the stack, but the memory ? How can this line trigger an overwrite operation on the memory ? I don't understand.
Thing is, is it proper that I see an operation in the window that results in no changes being made to the memory location I'm interested in ? Stack is pushed, that may be followed by changes to the memory area I'm interested in, in which case I do think that's the only part I should be seeing, not the cluster of instructions that led up to that final state. There being no references to memory locations in push instructions like push [eax] should make it impossible for it to affect the memory (not the region where stack resides) directly, should it not ? It's otherwise just an operation between the stack and registers.
I hope that's been comprehensive.
I'd like to state on a side note here that I do not know the precise implementation that makes keeping track of changes to a memory location possible. There may be cases that require inclusion of those follow-up instructions like you mentioned, yet I've not come across this type of situation before, hence I'm here asking. I'm assuming that this is either a known limitation or an oversight.
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 141 Reputation: 141
Joined: 06 Jul 2014
Posts: 4337
|
 Posted: Sun Apr 07, 2024 12:27 am Post subject: Posted: Sun Apr 07, 2024 12:27 am Post subject: |
 |
|
| Akillibirisi wrote: | | push esi will alter the stack, but the memory ? How can this line trigger an overwrite operation on the memory ? I don't understand. |
The stack is just an area of memory. The address you're looking at, 0019B740, is in the stack.
From a higher-level perspective, the "push" instruction pushes a value onto the stack.
From a lower-level perspective, the "push" instruction writes a value to a memory location specified by the ESP register.
Both of these explain how the "push" instruction works from different perspectives. I think you're only considering this from a higher-level perspective.
Some of those other instructions (`mov [esp+X],...` / `mov [ebp-X],...`) also write to the stack.
| Akillibirisi wrote: | | is it proper that I see an operation in the window that results in no changes being made to the memory location I'm interested in ? |
Some instructions (i.e. `jmp`, `nop`, `int 3`) are there due to a bug in CE that I've already explained. For all the other instructions (including `push`), they're in that window because they are writing to that address.
| Akillibirisi wrote: | | Stack is pushed, that may be followed by changes to the memory area I'm interested in, in which case I do think that's the only part I should be seeing, not the cluster of instructions that led up to that final state. |
I have no idea what you're talking about here. The stack doesn't get pushed- a value gets pushed onto the stack.
`push esi` - this pushes the value in ESI onto the stack. "Push a value onto the stack" means exactly this: make more space on the stack, and write the value into that space.
| Code: | push esi // push a value onto the stack
// same thing as:
sub esp,4 // make more space on the stack
mov [esp],esi // write the value into that space |
If ESP is 0019B744, then the instruction `push esi` will write to the address 0019B740. This is how the `push` instruction works. I don't know what kind of magic you think the stack is, but you're wrong. The stack is just an area of memory.
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
Akillibirisi
How do I cheat?
![]() Reputation: 0 Reputation: 0
Joined: 06 Jan 2019
Posts: 8
Location: Turkey
|
 Posted: Sun Apr 07, 2024 5:50 am Post subject: Posted: Sun Apr 07, 2024 5:50 am Post subject: |
 |
|
Well, I had completely ruled out the possibility that 0019B740 is a stack area, my bad there. I was expecting this address to hold some basic value like health, yet it turned out to be a highway of data that's being sent back and forth through.
Apart from that, I addressed stack and memory separately thinking it'd be more convenient though it seemingly backfired. I know stack is inside the memory, it's just the fact that said memory location happened to be the stack area that I failed to notice.
Stack is pushed, as in it expands to accommodate a new line on top, just a different interpretation of the same thing so chill out there.
Also thanks, I figured out the part of the ordeal caused by my oversight at the very least.
|
|
| Back to top |
|
 |
|
|
You cannot post new topics in this forum
You cannot reply to topics in this forum
You cannot edit your posts in this forum
You cannot delete your posts in this forum
You cannot vote in polls in this forum
You cannot attach files in this forum
You can download files in this forum
|
|

 Reputation: 141
Reputation: 141 Reputation: 141
Reputation: 141 Reputation: 141
Reputation: 141