|
Cheat Engine
The Official Site of Cheat Engine
|
| View previous topic :: View next topic |
| Author |
Message |
SuperAndromeda
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 30 Jul 2022
Posts: 12
|
 Posted: Sat Feb 24, 2024 12:51 am Post subject: Pointer's offset changes after every execution of the game Posted: Sat Feb 24, 2024 12:51 am Post subject: Pointer's offset changes after every execution of the game |
 |
|
Hello, I'm a beginner at CE, so take it easy on me.
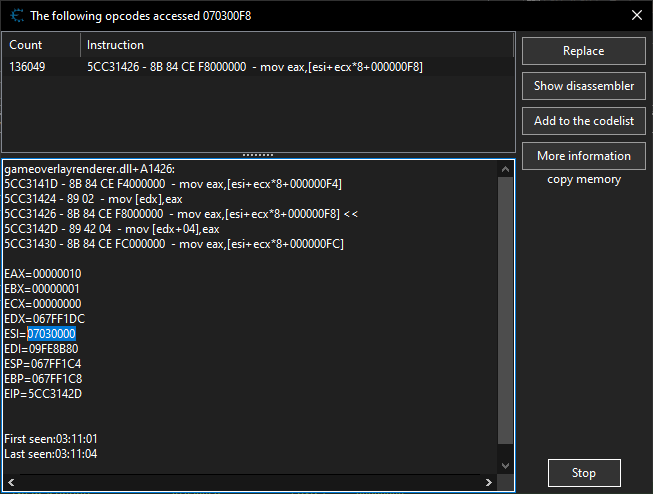
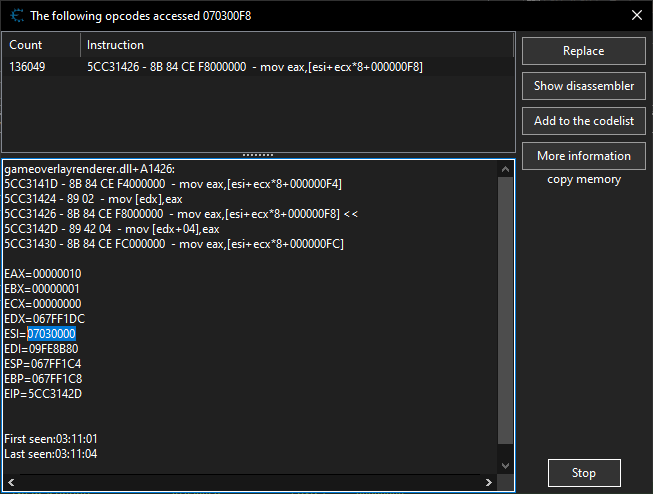
I got a green address after searching for "what access the target address" once. It is in the form of process-name.dll + address (gameoverlayrenderer.dll+10F684).
The values I want to control are the controller inputs for the 4 players of the game (Rivals of Aether), and each of them is distinguished by one offset of F8 plus a register times 8 (which is always a multiple of hex 10). The problem is, each time I open the game the offsets are redistributed. How do I get a pointer which has a fixed offset?
| Description: |
| Here is the accessing instruction list from the first address |
|
| Filesize: |
17.89 KB |
| Viewed: |
1143 Time(s) |
|
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 140 Reputation: 140
Joined: 06 Jul 2014
Posts: 4307
|
 Posted: Sat Feb 24, 2024 1:57 am Post subject: Posted: Sat Feb 24, 2024 1:57 am Post subject: |
 |
|
Try the pointer scanner.
https://www.youtube.com/watch?v=3dyIrcx8Z8g
If it really only goes through that data structure, you'll have to loop through each element in that array and figure out which one it is. Similar to step 9 of the CE tutorial.
Code injection is an alternative. Search "injection copy"
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
SuperAndromeda
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 30 Jul 2022
Posts: 12
|
 Posted: Sun Feb 25, 2024 9:06 am Post subject: Posted: Sun Feb 25, 2024 9:06 am Post subject: |
 |
|
| ParkourPenguin wrote: | Try the pointer scanner.
If it really only goes through that data structure, you'll have to loop through each element in that array and figure out which one it is. Similar to step 9 of the CE tutorial.
Code injection is an alternative. Search "injection copy" |
Unfortunately the pointer scanner doesn't return me any pointer after I restart the game.
So, I tried to look into the single instruction that access the 4 target addresses, each referring to one of the 4 players, and tried to search for commonalities and dissect data, but I couldn't find anything interesting among them (although I have never used this feature before), what could I do from here?
If I do code injection, how can write a code that can separate the address for each player, considering that the register will change every time the game opens?
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 140 Reputation: 140
Joined: 06 Jul 2014
Posts: 4307
|
 Posted: Sun Feb 25, 2024 12:36 pm Post subject: Posted: Sun Feb 25, 2024 12:36 pm Post subject: |
 |
|
When dissecting data, you can also look at the structures pointed to by pointers in the structure being dissected.
There are tons of walkthroughs going over step 9 of the CE tutorial if you want help or examples. Search on youtube.
Regarding code injection, you'd ideally find a better injection point. Specifically one that only accesses the address you want. If no such instructions access this address, try other addresses in the same structure. You only need a pointer to the structure itself- the offset to the address of the value you want will always be the same (0xF8).
If you can find something that distinguishes the address you want from those you don't (CE tutorial step 9), you could use that injection point anyway.
Also, when you said "offsets are redistributed", you were talking about ecx, right? esi changing is expected. ecx changing is not.
If you want the controller inputs for all 4 players and not just one specific player, isn't that pretty much what you already have? What other addresses does that instruction access?
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
SuperAndromeda
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 30 Jul 2022
Posts: 12
|
 Posted: Sun Feb 25, 2024 6:41 pm Post subject: Posted: Sun Feb 25, 2024 6:41 pm Post subject: |
 |
|
| ParkourPenguin wrote: | When dissecting data, you can also look at the structures pointed to by pointers in the structure being dissected.
There are tons of walkthroughs going over step 9 of the CE tutorial if you want help or examples. Search on youtube.
Regarding code injection, you'd ideally find a better injection point. Specifically one that only accesses the address you want. If no such instructions access this address, try other addresses in the same structure. You only need a pointer to the structure itself- the offset to the address of the value you want will always be the same (0xF8).
If you can find something that distinguishes the address you want from those you don't (CE tutorial step 9), you could use that injection point anyway.
Also, when you said "offsets are redistributed", you were talking about ecx, right? esi changing is expected. ecx changing is not.
If you want the controller inputs for all 4 players and not just one specific player, isn't that pretty much what you already have? What other addresses does that instruction access? |
Yes, the real problem is ECX. It has a different fixed value for each player for the entire execution but this value changes after the next reopening. For example, in the first startup, player 1 can have ECX = 0, player 2 has ECX = 2, player 3 has 4 and player 4 has 6, but in the next time the values are swapped in a way it's not possible to predict.
|
|
| Back to top |
|
 |
SuperAndromeda
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 30 Jul 2022
Posts: 12
|
 Posted: Tue Mar 05, 2024 12:07 pm Post subject: Posted: Tue Mar 05, 2024 12:07 pm Post subject: |
 |
|
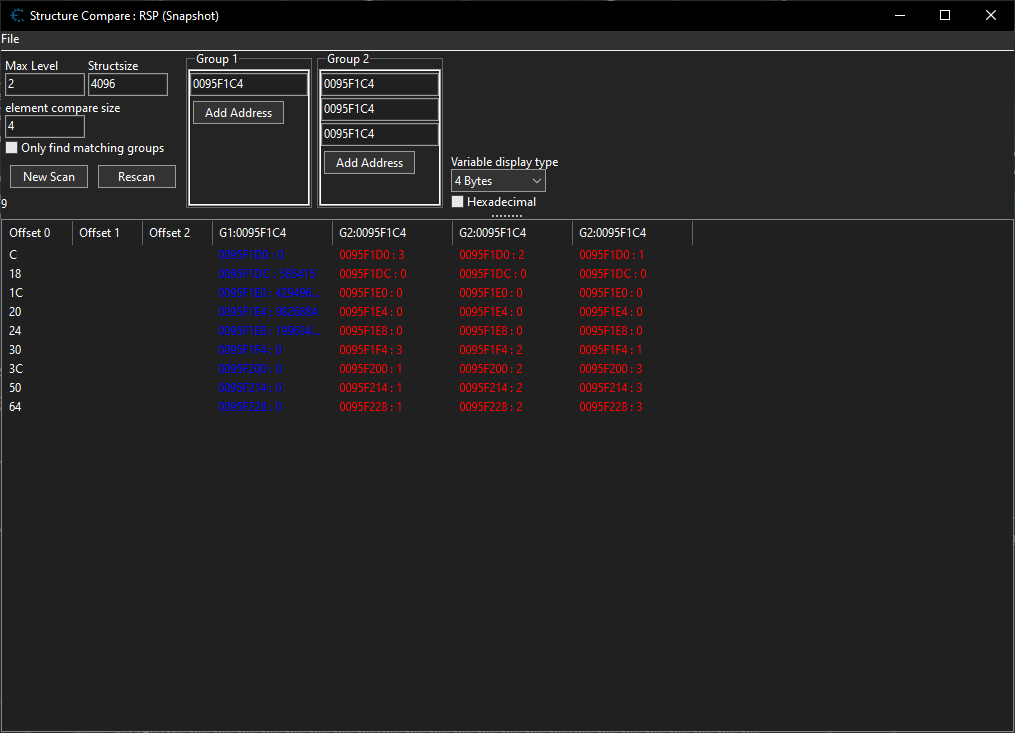
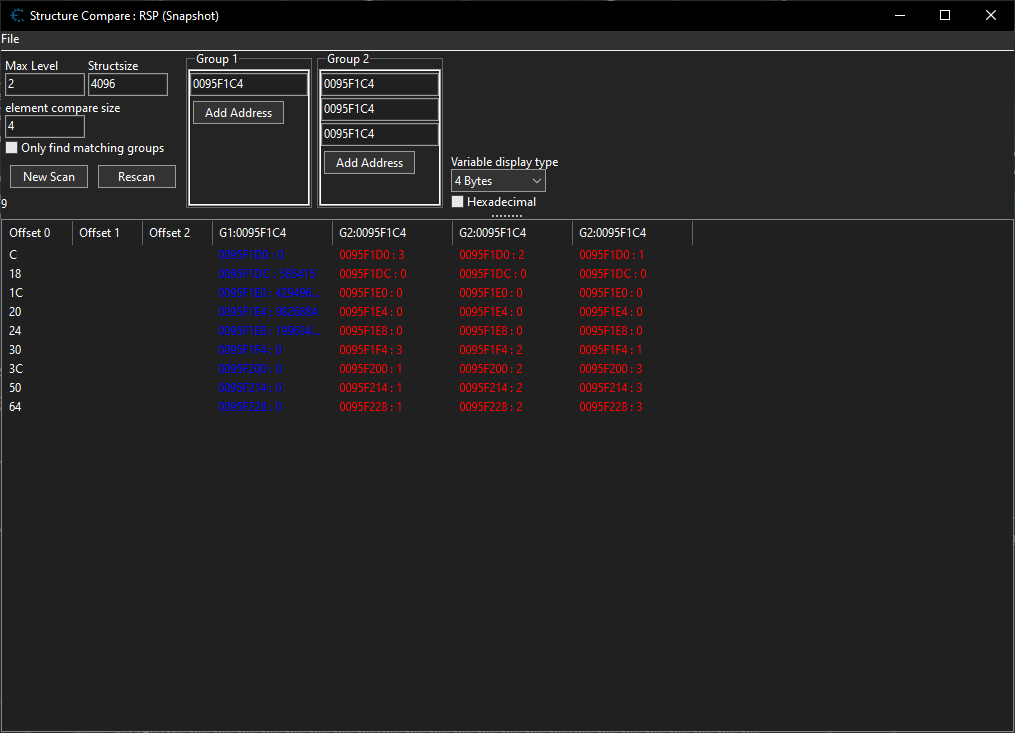
So, I managed to find a commonality among the 4 addresses that distinguishes each player (offset C), but it's in the RSP (Snapshot). Do you think it can work?
If it does, do you think I can inject a code in which I can move values to a fixed address according to the value of RSP+C?
| Description: |
|
| Filesize: |
36.97 KB |
| Viewed: |
693 Time(s) |
|
|
|
| Back to top |
|
 |
ParkourPenguin
I post too much
 Reputation: 140 Reputation: 140
Joined: 06 Jul 2014
Posts: 4307
|
 Posted: Tue Mar 05, 2024 1:02 pm Post subject: Posted: Tue Mar 05, 2024 1:02 pm Post subject: |
  |
|
ESP is the stack pointer. I'd need to look at more of the original code to see if it's technically safe, but you can try it anyway.
Just watch out for instructions that modify ESP. e.g. if you're backing up a register with push/pop, you'll need to change the offset accordingly.
| Code: | mov eax,[esp+C]
push ebx
mov eax,[esp+10] // same address / value |
PS: RSP is for 64-bit code, ESP is for 32-bit code. In 64-bit code, push / pop / call / ret modifies RSP by 8 bytes; in 32-bit code, it's 4 bytes.
Here, CE probably displays RSP because mostly everything is 64-bit now (32-bit mnemonics were neglected). It could also be some WOW64 thing I don't know about.
_________________
I don't know where I'm going, but I'll figure it out when I get there. |
|
| Back to top |
|
 |
|
|
You cannot post new topics in this forum
You cannot reply to topics in this forum
You cannot edit your posts in this forum
You cannot delete your posts in this forum
You cannot vote in polls in this forum
You cannot attach files in this forum
You can download files in this forum
|
|

 Reputation: 140
Reputation: 140 Reputation: 140
Reputation: 140 Reputation: 140
Reputation: 140