| View previous topic :: View next topic |
| Author |
Message |
erfg1
Cheater
 Reputation: 0 Reputation: 0
Joined: 14 Jul 2013
Posts: 49
|
 Posted: Wed Feb 22, 2017 10:30 pm Post subject: AoB store address and write to it Posted: Wed Feb 22, 2017 10:30 pm Post subject: AoB store address and write to it |
 |
|
I want to be able to write to an address's value and find it via AoB scan.
When I try to save this script it says it won't be able to inject. I have been searching up and down for a solution but I cannot locate anything about it.
| Code: | [ENABLE]
//code from here to '[DISABLE]' will be used to enable the cheat
alloc(newmem,2048)
label(returnhere)
label(exit)
newmem: //this is allocated memory, you have read,write,execute access
aobscan(findit,88 86 87 00 00 00 E8 F1 FA FF FF 84 C0 0F 94 C0)
movss [ecx+1C],xmm0
push eax
mov eax,(float)1908
mov [findit],eax
pop eax
exit:
jmp returnhere
//"Game.dll"+3DA35
aobscan(start,F3 0F 11 41 1C F3 0F 10 41 24 F3 0F 58 C1 F3 0F)
start:
jmp newmem
returnhere:
[DISABLE]
//code from here till the end of the code will be used to disable the cheat
dealloc(newmem)
"Game.dll"+3DA35:
movss [ecx+1C],xmm0 |
_________________
|
|
| Back to top |
|
 |
SunBeam
I post too much
 Reputation: 65 Reputation: 65
Joined: 25 Feb 2005
Posts: 4022
Location: Romania
|
 Posted: Thu Feb 23, 2017 7:48 am Post subject: Posted: Thu Feb 23, 2017 7:48 am Post subject: |
 |
|
Try this:
| Code: | [ENABLE]
aobscanmodule( findit, Game.dll, 888687000000E8F1FAFFFF84C00F94C0 )
registersymbol( findit )
alloc( newmem, 2048, Game.dll )
label( PTR )
registersybmol( PTR )
label( const )
label( back )
newmem:
movss [ecx+1C],xmm0
push eax
mov [PTR],ecx // store pointer
mov eax,[const] // get 1908
mov [ecx+1C],eax // write it
pop eax
jmp back
const:
dd (float)1908
//"Game.dll"+3DA35
findit:
jmp newmem
back:
// add NOPs here to normalize code
[DISABLE]
//"Game.dll"+3DA35:
findit:
movss [ecx+1C],xmm0
unregistersybmol( PTR )
dealloc( newmem )
unregistersymbol( findit ) |
You can now add a new address to the list, type in PTR and give it a name. This will be your base pointer. Adding 1 level to it, offset 1C, would point to your location where you want to write the 1908.
BR,
Sun
|
|
| Back to top |
|
 |
erfg1
Cheater
 Reputation: 0 Reputation: 0
Joined: 14 Jul 2013
Posts: 49
|
 Posted: Thu Feb 23, 2017 4:20 pm Post subject: Posted: Thu Feb 23, 2017 4:20 pm Post subject: |
 |
|
I tried modifying it a bit but the game froze.
| Code: | [ENABLE]
aobscanmodule( findit, Game.dll, 888687000000E8F1FAFFFF84C00F94C0 )
registersymbol( findit )
alloc( newmem, 2048, Game.dll )
registersymbol( PTR )
//label( PTR )
alloc(PTR,4)
label( const )
label( back )
newmem:
movss [ecx+1C],xmm0
push eax
mov [PTR],ecx // store pointer
mov eax,[const] // get 1908
mov [ecx+1C],eax // write it
pop eax
jmp back
const:
dd (float)1908
//"Game.dll"+3DA35
findit:
jmp newmem
back:
// add NOPs here to normalize code
[DISABLE]
//"Game.dll"+3DA35:
findit:
movss [ecx+1C],xmm0
//unregistersybmol( PTR )
dealloc( newmem )
unregistersymbol( findit ) |
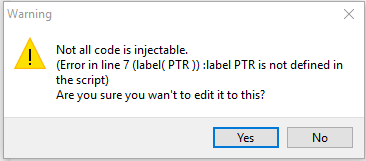
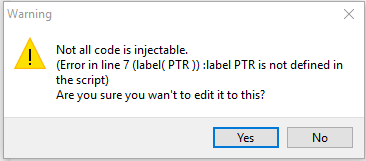
There was an error when trying to save the script you provided:
| Description: |
|
| Filesize: |
5.04 KB |
| Viewed: |
14052 Time(s) |
|
_________________
|
|
| Back to top |
|
 |
SunBeam
I post too much
 Reputation: 65 Reputation: 65
Joined: 25 Feb 2005
Posts: 4022
Location: Romania
|
 Posted: Thu Feb 23, 2017 5:26 pm Post subject: Posted: Thu Feb 23, 2017 5:26 pm Post subject: |
 |
|
Forgot to declare PTR:
| Code: | [ENABLE]
aobscanmodule( findit, Game.dll, 888687000000E8F1FAFFFF84C00F94C0 )
registersymbol( findit )
alloc( newmem, 2048, Game.dll )
label( PTR )
registersybmol( PTR )
label( const )
label( back )
newmem:
movss [ecx+1C],xmm0
push eax
mov [PTR],ecx // store pointer
mov eax,[const] // get 1908
mov [ecx+1C],eax // write it
pop eax
jmp back
const:
dd (float)1908
PTR:
dd 0
//"Game.dll"+3DA35
findit:
jmp newmem
back:
[DISABLE]
//"Game.dll"+3DA35:
findit:
movss [ecx+1C],xmm0
unregistersybmol( PTR )
dealloc( newmem )
unregistersymbol( findit ) |
Make sure the aobscan pattern "888687000000E8F1FAFFFF84C00F94C0" is unique. If there's too many results found, you'll have to add to it to make it unique.
BR,
Sun
|
|
| Back to top |
|
 |
erfg1
Cheater
 Reputation: 0 Reputation: 0
Joined: 14 Jul 2013
Posts: 49
|
 Posted: Thu Feb 23, 2017 6:19 pm Post subject: Posted: Thu Feb 23, 2017 6:19 pm Post subject: |
 |
|
Here is my modified code:
| Code: | [ENABLE]
aobscanmodule( findit, Game.dll, ??????????000000000000000000C84101??????0000964300003944 )
registersymbol( findit )
alloc( newmem, 2048, Game.dll )
label( PTR )
registersymbol( PTR )
label( const )
label( back )
newmem:
movss [ecx+1C],xmm0
push eax
mov [PTR],ecx // store pointer
mov eax,[const] // get 1908
mov [ecx+1C],eax // write it
pop eax
jmp back
const:
dd (float)1908
PTR:
dd 0
//"Game.dll"+3DA35
findit:
jmp newmem
back:
[DISABLE]
//"Game.dll"+3DA35:
findit:
movss [ecx+1C],xmm0
unregistersymbol( PTR )
dealloc( newmem )
unregistersymbol( findit ) |
The active checkbox cant be checked so something must be wrong.
_________________
|
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Thu Feb 23, 2017 6:28 pm Post subject: Posted: Thu Feb 23, 2017 6:28 pm Post subject: |
 |
|
| Quote: | | ??????????000000000000000000C84101??????0000964300003944 |
FYI - any wildcard variables at the beginning or end of an AOB signature serve no purpose.
|
|
| Back to top |
|
 |
erfg1
Cheater
 Reputation: 0 Reputation: 0
Joined: 14 Jul 2013
Posts: 49
|
 Posted: Thu Feb 23, 2017 10:07 pm Post subject: Posted: Thu Feb 23, 2017 10:07 pm Post subject: |
 |
|
I'm pretty new to the scripting system in cheat engine, but I saw something about LUA and ASM can be on the same script. So, I made this...
| Code: | [ENABLE]
{$lua}
local res = AOBScan("?? ?? ?? ?? ?? 00 00 00 00 00 00 00 00 00 C8 41 01 ?? ?? ?? 00 00 96 43 00 00 ?? ?? 00 00 00 00 00 00 00 00 BC 5F ?? 56 ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? 00 00 00 00 BC 5F ?? 56 ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? 00 00 00 00 00 00 00 00 00 00 48 42 00 00 48 42 00 00 48 42 00 00 7A 4300 00 7A 43 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 96 43 00 00 00 00 1F 85 6B 3F 00 00 A0 3F 00 00 A0 3F CD CC 4C BD 00 00 82 42")
if res == nil then return end
registerSymbol('myCurHP',res[0])
{$asm}
[DISABLE]
unregistersymbol(myCurHP)
dealloc(myCurHP) |
Now I can use myCurHP for my characters HP.
_________________
|
|
| Back to top |
|
 |
SunBeam
I post too much
 Reputation: 65 Reputation: 65
Joined: 25 Feb 2005
Posts: 4022
Location: Romania
|
 Posted: Fri Feb 24, 2017 4:46 am Post subject: Posted: Fri Feb 24, 2017 4:46 am Post subject: |
 |
|
| So, you're still in need of help or figured it out?..
|
|
| Back to top |
|
 |
erfg1
Cheater
 Reputation: 0 Reputation: 0
Joined: 14 Jul 2013
Posts: 49
|
 Posted: Fri Feb 24, 2017 7:23 am Post subject: Posted: Fri Feb 24, 2017 7:23 am Post subject: |
 |
|
Only issue I'm having is unregistering the symbol. I run an lua script to unregistered it but it won't do it.
Also, do lua scripts auto execute when you open the .CT files?
_________________
|
|
| Back to top |
|
 |
SunBeam
I post too much
 Reputation: 65 Reputation: 65
Joined: 25 Feb 2005
Posts: 4022
Location: Romania
|
 Posted: Fri Feb 24, 2017 8:20 am Post subject: Posted: Fri Feb 24, 2017 8:20 am Post subject: |
 |
|
| If symbol was not registered to begin with, then unregistering won't work. As for LUA, scripts do auto-run; you can disable this in CE's settings (General Settings -> Ask to run lua scripts from tables; Always run lua scripts from tables).
|
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Fri Feb 24, 2017 9:59 am Post subject: Posted: Fri Feb 24, 2017 9:59 am Post subject: |
 |
|
| erfg1 wrote: | | Code: | [ENABLE]
{$lua}
local res = AOBScan("?? ?? ?? ?? ?? 00 00 00 00 00 00 00 00 00 C8 41 01 ?? ?? ?? 00 00 96 43 00 00 ?? ?? 00 00 00 00 00 00 00 00 BC 5F ?? 56 ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? 00 00 00 00 BC 5F ?? 56 ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? 00 00 00 00 00 00 00 00 00 00 48 42 00 00 48 42 00 00 48 42 00 00 7A 4300 00 7A 43 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 96 43 00 00 00 00 1F 85 6B 3F 00 00 A0 3F 00 00 A0 3F CD CC 4C BD 00 00 82 42")
if res == nil then return end
registerSymbol('myCurHP',res[0])
{$asm}
[DISABLE]
unregistersymbol(myCurHP)
dealloc(myCurHP) |
|
| ++METHOS wrote: | | Quote: | | ??????????000000000000000000C84101??????0000964300003944 |
FYI - any wildcard variables at the beginning or end of an AOB signature serve no purpose. |
|
|
| Back to top |
|
 |
STN
I post too much
 Reputation: 42 Reputation: 42
Joined: 09 Nov 2005
Posts: 2672
|
 Posted: Fri Feb 24, 2017 11:03 am Post subject: Posted: Fri Feb 24, 2017 11:03 am Post subject: |
 |
|
| ++METHOS wrote: | | erfg1 wrote: | | Code: | [ENABLE]
{$lua}
local res = AOBScan("?? ?? ?? ?? ?? 00 00 00 00 00 00 00 00 00 C8 41 01 ?? ?? ?? 00 00 96 43 00 00 ?? ?? 00 00 00 00 00 00 00 00 BC 5F ?? 56 ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? 00 00 00 00 BC 5F ?? 56 ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? ?? 00 00 00 00 00 00 00 00 00 00 48 42 00 00 48 42 00 00 48 42 00 00 7A 4300 00 7A 43 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 96 43 00 00 00 00 1F 85 6B 3F 00 00 A0 3F 00 00 A0 3F CD CC 4C BD 00 00 82 42")
if res == nil then return end
registerSymbol('myCurHP',res[0])
{$asm}
[DISABLE]
unregistersymbol(myCurHP)
dealloc(myCurHP) |
|
| ++METHOS wrote: | | Quote: | | ??????????000000000000000000C84101??????0000964300003944 |
FYI - any wildcard variables at the beginning or end of an AOB signature serve no purpose. |
|
I guess he wants to start from the first byte (res:) even if ignoring it instead of adding offsets (res+1234:).
Or maybe he doesn't understand what you're talking about.
_________________
|
|
| Back to top |
|
 |
erfg1
Cheater
 Reputation: 0 Reputation: 0
Joined: 14 Jul 2013
Posts: 49
|
 Posted: Fri Feb 24, 2017 1:14 pm Post subject: Posted: Fri Feb 24, 2017 1:14 pm Post subject: |
 |
|
@SunBeam I think it's currently registered. How can I tell? It shows the old address it used to be when I made the LUA script the first time. I want it to unregister and then re-register.
@STN @++METHOS Yup, I put the byte masks there so it would start at that address.
_________________
|
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Fri Feb 24, 2017 1:20 pm Post subject: Posted: Fri Feb 24, 2017 1:20 pm Post subject: |
  |
|
| erfg1 wrote: | | @SunBeam I think it's currently registered. How can I tell? |
-In memory viewer, Ctrl+U to bring up user-defined symbols.
|
|
| Back to top |
|
 |
erfg1
Cheater
 Reputation: 0 Reputation: 0
Joined: 14 Jul 2013
Posts: 49
|
 Posted: Fri Feb 24, 2017 3:56 pm Post subject: Posted: Fri Feb 24, 2017 3:56 pm Post subject: |
 |
|
@++METHOS Thanks! That helped a lot!
Looks like when I save the .CT after applying the lua script that symbol is saved along with it.
I was using...
| Code: | [DISABLE]
unregisterSymbol(myCurHP) |
which was wrong, I should have used..
| Code: | [DISABLE]
unregisterSymbol('myCurHP') |
So my problem is fixed. Thanks everyone who helped me! 
_________________
|
|
| Back to top |
|
 |
|

 Reputation: 0
Reputation: 0 Reputation: 65
Reputation: 65 Reputation: 0
Reputation: 0 Reputation: 65
Reputation: 65 Reputation: 0
Reputation: 0 Reputation: 0
Reputation: 0 Reputation: 65
Reputation: 65 Reputation: 0
Reputation: 0 Reputation: 65
Reputation: 65 Reputation: 42
Reputation: 42 Reputation: 0
Reputation: 0 Reputation: 0
Reputation: 0