|
Cheat Engine
The Official Site of Cheat Engine
|
| View previous topic :: View next topic |
| Author |
Message |
Punz1A4
Cheater
![]() Reputation: 0 Reputation: 0
Joined: 10 Jun 2016
Posts: 25
|
 Posted: Sat Jan 07, 2017 9:10 am Post subject: Problematic opcode - changing pointer Posted: Sat Jan 07, 2017 9:10 am Post subject: Problematic opcode - changing pointer |
 |
|
I was writing a simple asm script that worked until I rebooted the game.
Figured it was a problem with aobscanmodule - had to replace few bytes with ??. Script started to work again, but when I turned it off some values in game i was changing got messed up.
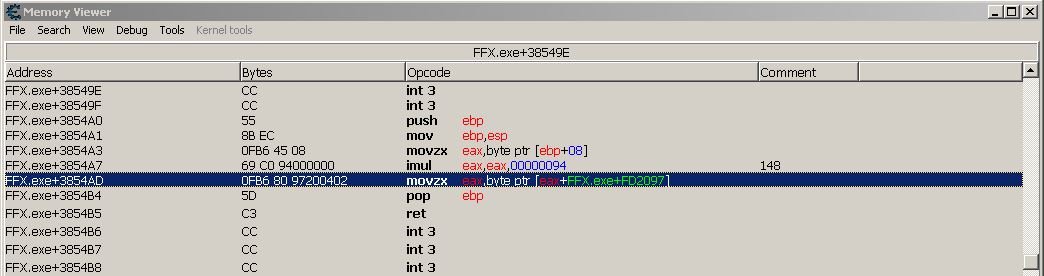
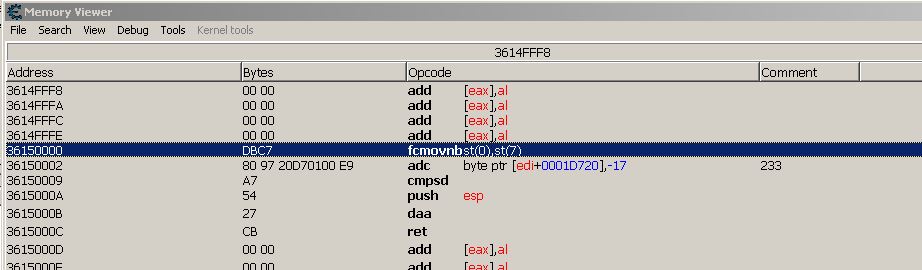
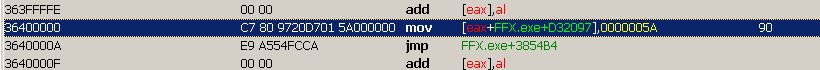
Dug a little deeper and it seems the problem lies with the way one line of op code is constructed (highlighted on screenshot)
The issue is that the offset of eax (here FFX.exe+FD2097) keeps changing each time I reboot the game.
Now not really problematic when I enable the script cause it simply removes that opcode, however when I disable the script wrong opcode is restored.
TL;DR Is it possible to automatically store the original opcode each time before enabling the script and the restoring it in disable section?
Or maybe any other way it can be fixed?
Here's the script I wrote:
| Code: | [ENABLE]
aobscanmodule(inf_s_lv,FFX.exe,0F B6 80 97 20 ?? ?? 5D C3) // should be unique
alloc(newmem,$1000)
label(code)
label(return)
newmem:
code:
//movzx eax,byte ptr [eax+FFX.exe+D32097]
mov eax,#90
jmp return
inf_s_lv:
jmp newmem
nop
nop
return:
registersymbol(inf_s_lv)
[DISABLE]
inf_s_lv:
db 0F B6 80 97 20 04 02 // this restores movzx eax,byte ptr [eax+FFX.exe+D32097] which isn't correct after I reboot the game
unregistersymbol(inf_s_lv)
dealloc(newmem) |
(It was written on previous instance of the running game so the offset in the script is different than on the picture and that's the problem I'm trying to fix)
| Description: |
|
| Filesize: |
57.24 KB |
| Viewed: |
6172 Time(s) |
|
|
|
| Back to top |
|
 |
Zanzer
I post too much
![]() Reputation: 126 Reputation: 126
Joined: 09 Jun 2013
Posts: 3278
|
 Posted: Sat Jan 07, 2017 9:21 am Post subject: Posted: Sat Jan 07, 2017 9:21 am Post subject: |
 |
|
| Code: | [ENABLE]
aobscanmodule(inf_s_lv,FFX.exe,0F B6 80 ?? ?? ?? ?? 5D C3)
alloc(newmem,$1000)
label(s_lv_bkp)
label(return)
newmem:
s_lv_bkp:
reassemble(inf_s_lv)
mov eax,#90
jmp return
inf_s_lv:
jmp newmem
nop
nop
return:
registersymbol(inf_s_lv)
registersymbol(s_lv_bkp)
[DISABLE]
inf_s_lv:
reassemble(s_lv_bkp)
unregistersymbol(inf_s_lv)
unregistersymbol(s_lv_bkp)
dealloc(newmem) |
|
|
| Back to top |
|
 |
Punz1A4
Cheater
![]() Reputation: 0 Reputation: 0
Joined: 10 Jun 2016
Posts: 25
|
 Posted: Sat Jan 07, 2017 10:29 am Post subject: Posted: Sat Jan 07, 2017 10:29 am Post subject: |
 |
|
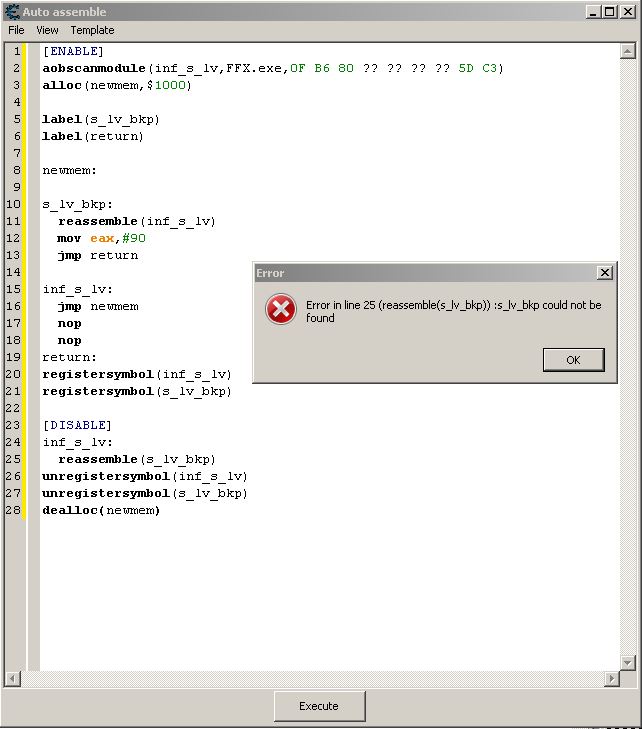
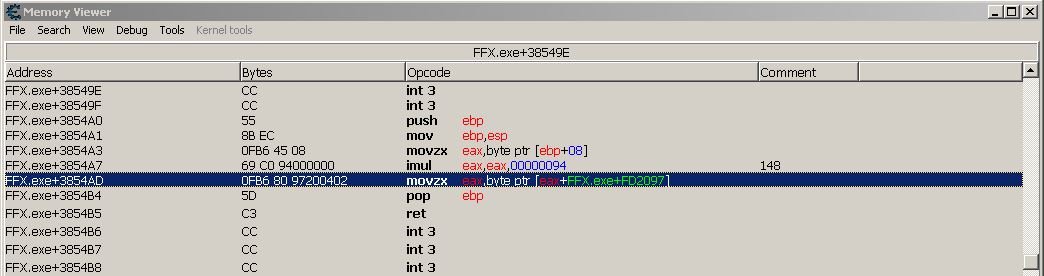
Thanks for the quick answer Zanzer 
So there was an error for some reason as seen in the attachment, however i did some research bout reassemble and readmem and managed to fix it somehow. I also had to increase bytes in aobscanmodule cause it was picking some other instructions/
A new problem has arisen though :/ It seems that mov eax,#90 does work but only while script is active and after turning it off the value gets reverted to whatever it was before activating the script.
So it seems that i have to edit the value of the address with the chaning offset ([eax+FFX.exe+D32097]) after all. Is this possible thing to do?
I've read a bit about it in lua forums and came across this:
| Code: | | addresstring,opcode,bytes,extra=splitDisassembledString(disassemble("FFX.exe+3854AD")) |
Though opcode variable returns entire opcode as string and I don't really know what to do next...
Any ideas ? 
Oh and that's the way I fixed the code btw.
| Code: | [ENABLE]
aobscanmodule(inf_s_lv,FFX.exe,69 C0 94 00 00 00 0F B6 80 ?? ?? ?? ?? 5D C3) // should be unique
alloc(newmem,$1000)
label(code)
label(return)
alloc(originalbytes, 7)
registersymbol(originalbytes)
originalbytes:
readmem(inf_s_lv+6,7)
newmem:
code:
//movzx eax,byte ptr [eax+FFX.exe+D32097]
reassemble(inf_s_lv+6)
mov eax,#90
jmp return
inf_s_lv+6:
jmp newmem
nop
nop
return:
registersymbol(inf_s_lv)
[DISABLE]
inf_s_lv+6:
readmem(originalbytes, 7)
unregistersymbol(inf_s_lv)
dealloc(newmem)
unregistersymbol(originalbytes)
dealloc(originalbytes) |
EDIT:
So I'm no expert at assembly but it seems that command
| Code: | | mov [eax+FFX.exe+D32097],#90 |
always has byte code C7 80 ?? ?? ?? ?? 5A000000 where the question marks are depending on the offset in [eax+FFX.exe+D32097]. I can get value of those question marks by running
| Code: | changing_bytes:
readmem(inf_s_lv+9,4) |
I just don't know if it's possible to add C7 80 to the "left side" of changing_bytes value and 5A000000 to the "right side". Then I can just reassemble(chaning_bytes) to get
| Code: | | mov whatever-the-offset-is,#90 |
right? Just a thought but if it's correct then how can I add bytes to changing_bytes value?
| Description: |
|
| Filesize: |
67.23 KB |
| Viewed: |
6146 Time(s) |
|
|
|
| Back to top |
|
 |
Zanzer
I post too much
![]() Reputation: 126 Reputation: 126
Joined: 09 Jun 2013
Posts: 3278
|
 Posted: Sat Jan 07, 2017 11:01 am Post subject: Posted: Sat Jan 07, 2017 11:01 am Post subject: |
 |
|
See if this works out. | Code: | code:
db C6 80
readmem(inf_s_lv+9,4)
db 5A
mov eax,#90
jmp return |
Basically, we are building the following instruction using bytes. | Code: | | mov byte ptr [eax+FFX.exe+D32097],#90 |
|
|
| Back to top |
|
 |
Punz1A4
Cheater
![]() Reputation: 0 Reputation: 0
Joined: 10 Jun 2016
Posts: 25
|
 Posted: Sat Jan 07, 2017 11:09 am Post subject: Posted: Sat Jan 07, 2017 11:09 am Post subject: |
 |
|
| Code: | code:
db db C6 80
readmem(inf_s_lv+9,4)
db 5A
//mov eax,#90
jmp return |
aswell as
| Code: | code:
db db C6 80
readmem(inf_s_lv+9,4)
db 5A
mov eax,#90
jmp return |
seems to be crashing my game 100% of the time :/
Didn't change anything else from previous script.
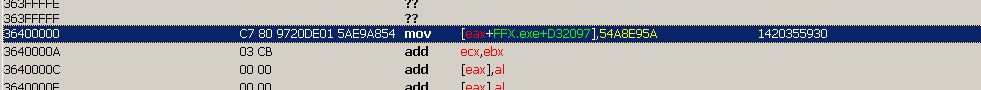
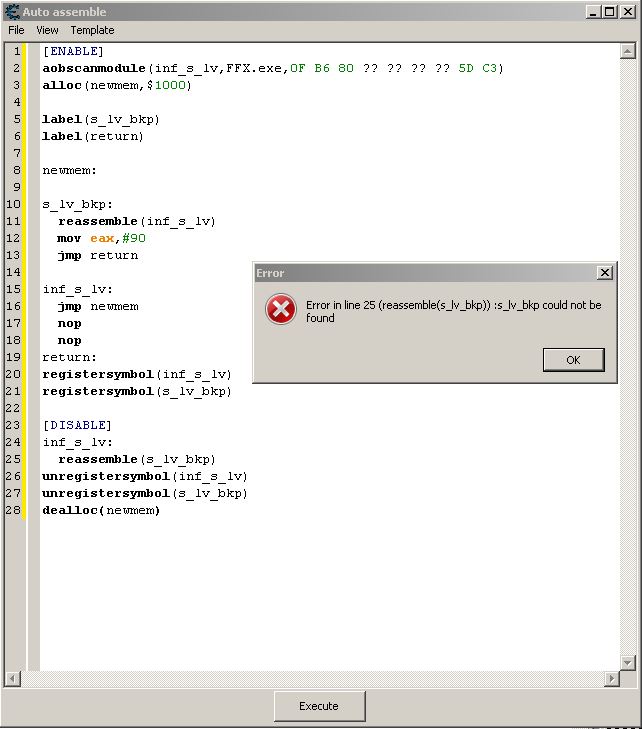
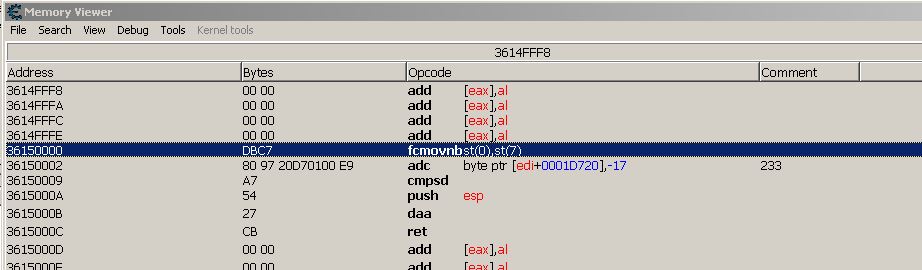
EDIT (picture3):
Well turns out it doesn't crash if I reboot the game and don't open the interface which is affected by code we're modifying.
However the thing that gets injected looks very weird.
Also no other scripts are running at the same time (just a heads up).
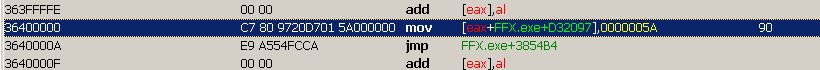
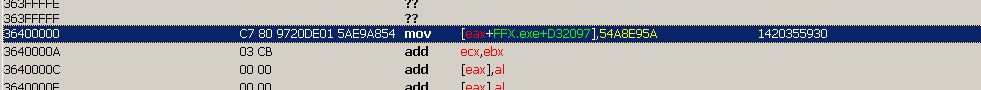
EDIT2 (picture4):
Posted the screenshot of mov [eax+FFX.exe+D32097],#90 in memory viewer inserted "manually" in a different script ... still no idea what is wrong with the script. :/
EDIT3...(picture5):
It seems like I typed db twice by accident like in i quoted originally... still crashing after fixing it and still getting some (a bit less) weird code injected.
Also why is there no return (jmp back) in injected code  it is in the script. it is in the script.
EDIT4(i feel like those lonely ppl talking to themselves in drama movies lol):
Anyway I think I fixed it... I decided to smack some random nops (db 90) here and there and although it didn't help exactly help, it did show me where lied the problem - this is the script that works how intended:
| Code: | code:
db C7 80
readmem(inf_s_lv+9,4)
db 5A
db 00
db 00
db 00
mov eax,#90
jmp return |
dunno why you can't just go with db 5A000000 and it has to be split in 4 parts... anyway that'd be it - thanks to Zanzer for helping me figure it out 
| Description: |
|
| Filesize: |
25.86 KB |
| Viewed: |
6111 Time(s) |
|
| Description: |
|
| Filesize: |
23.95 KB |
| Viewed: |
6119 Time(s) |
|
| Description: |
|
| Filesize: |
48.34 KB |
| Viewed: |
6125 Time(s) |
|
|
|
| Back to top |
|
 |
Zanzer
I post too much
![]() Reputation: 126 Reputation: 126
Joined: 09 Jun 2013
Posts: 3278
|
 Posted: Sat Jan 07, 2017 3:15 pm Post subject: Posted: Sat Jan 07, 2017 3:15 pm Post subject: |
 |
|
You can use DD to enter a 4-byte value.
Also be aware that the original size of that variable is only 1-byte.
By writing 4 bytes into it, you may be overwriting 3 other 1-byte variables that came after.
That is why my script used C6 instead of C7.
| Code: | code:
db C6 80 // 1-byte
readmem(inf_s_lv+9,4)
db #90 // 1-byte
mov eax,#90
jmp return |
| Code: | code:
db C7 80 // 4-byte
readmem(inf_s_lv+9,4)
dd #90 // 4-byte
mov eax,#90
jmp return |
|
|
| Back to top |
|
 |
Punz1A4
Cheater
![]() Reputation: 0 Reputation: 0
Joined: 10 Jun 2016
Posts: 25
|
 Posted: Sun Jan 08, 2017 10:05 am Post subject: Posted: Sun Jan 08, 2017 10:05 am Post subject: |
 |
|
Yeah, I kind of did something similar through trial and arror before you posted, by checking what's the byte code for
| Code: | | mov byte ptr [eax+FFX.exe+D32097],#99 |
(turns out I missed the byte ptr part in your second post ^^)
So I had something like this in the end:
| Code: | code:
// mov byte ptr [eax+FFX.exe+D32097],#99:
db C6 80
readmem(inf_s_lv+9,4)
db 63
// movzx eax,byte ptr [eax+FFX.exe+D32097]:
db 0F B6 80
readmem(inf_s_lv+9,4)
jmp return |
The old stuff was indeed overwriting to many bytes because at some point I mysteriously lost the ability to execute basic attacks in the game  . .
Anyway thanks for explaining the db dd difference 
|
|
| Back to top |
|
 |
|
|
You cannot post new topics in this forum
You cannot reply to topics in this forum
You cannot edit your posts in this forum
You cannot delete your posts in this forum
You cannot vote in polls in this forum
You cannot attach files in this forum
You can download files in this forum
|
|