| View previous topic :: View next topic |
| Author |
Message |
Nicholas Cage
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 18 Apr 2014
Posts: 16
Location: no
|
 Posted: Sun Apr 20, 2014 10:35 pm Post subject: Printing an opcode's AoB? Posted: Sun Apr 20, 2014 10:35 pm Post subject: Printing an opcode's AoB? |
 |
|
Yeah.
When I search for 0xD9, 0x04, 0x24, 0x59, 0xC3, 0x8B, 0x91, 0xF0, 0x01, 0x00, 0x00, 0xF3, 0x0F it brings up 00C9AB62.
And when I look at its bytes, it shows up FF 24 85 50ADC900.
I'm really new at exploiting, so yeah.
Is there a way to convert bytes into AoB?
Thanks for reading or responding in advance.
|
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Sun Apr 20, 2014 11:03 pm Post subject: Posted: Sun Apr 20, 2014 11:03 pm Post subject: |
 |
|
AOB = array of bytes.
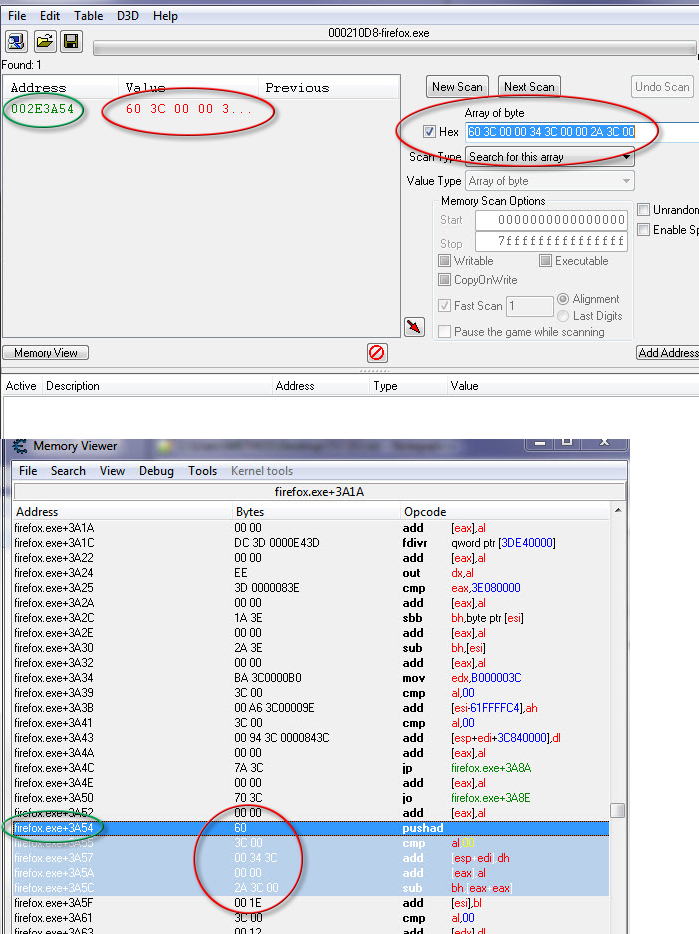
Green is address, red is bytes:
|
|
| Back to top |
|
 |
Nicholas Cage
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 18 Apr 2014
Posts: 16
Location: no
|
 Posted: Mon Apr 21, 2014 12:59 pm Post subject: Posted: Mon Apr 21, 2014 12:59 pm Post subject: |
 |
|
The AOB on it says FF 24 85 50 AD 50 01 8A 86 A4, but on the one in the table it says other wise.
WAT IS THIS BLACK MAGIC
|
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Mon Apr 21, 2014 2:52 pm Post subject: Posted: Mon Apr 21, 2014 2:52 pm Post subject: |
 |
|
Not sure what you're referring to...however...it could be that the code is changing. In order to remedy this, we use wildcard variables. As an example:
FF 24 85 50 AD ?? ?? 8A ?? A4
If that is not the case, then it could be that the table that you are referring to was created for a different version/release of the target.
|
|
| Back to top |
|
 |
Nicholas Cage
Newbie cheater
![]() Reputation: 0 Reputation: 0
Joined: 18 Apr 2014
Posts: 16
Location: no
|
 Posted: Mon Apr 21, 2014 3:06 pm Post subject: Posted: Mon Apr 21, 2014 3:06 pm Post subject: |
 |
|
I meant as in
blah = {0xD9, 0x04, 0x24, 0x59, 0xC3, 0x8B, 0x91, 0xF0, 0x01, 0x00, 0x00, 0xF3, 0x0F}
It leads to 0150ab62.
The bytes on the side of it says FF 24 85 50 AD 50 01 8A 86 A4.
That's why I'm confused.
And thanks, i'll try it out.
|
|
| Back to top |
|
 |
++METHOS
I post too much
![]() Reputation: 92 Reputation: 92
Joined: 29 Oct 2010
Posts: 4197
|
 Posted: Mon Apr 21, 2014 6:59 pm Post subject: Posted: Mon Apr 21, 2014 6:59 pm Post subject: |
 |
|
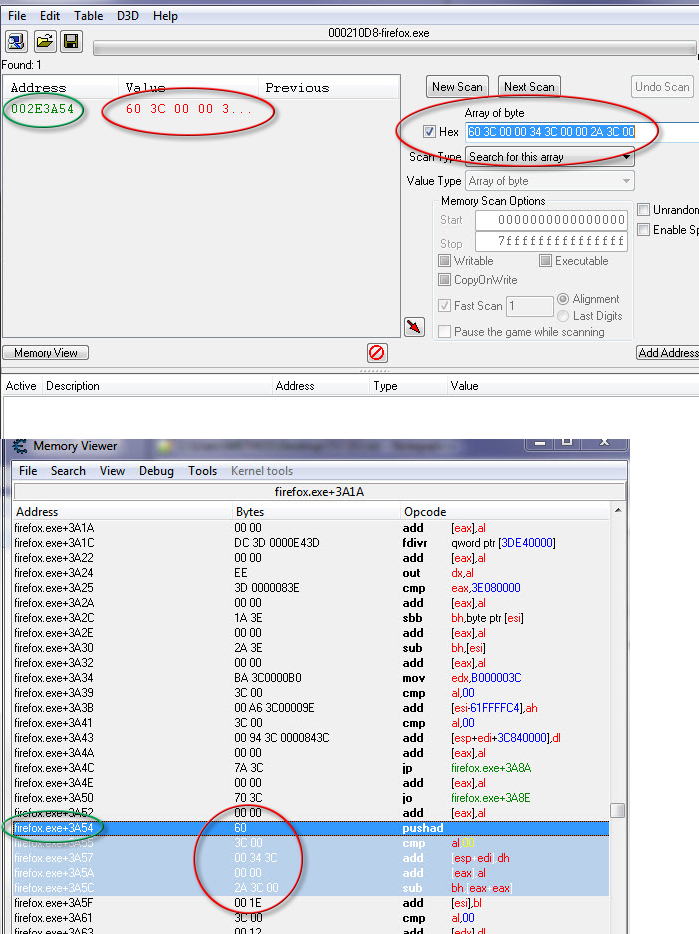
| Not sure what you're doing. When you scan for AOB, in the results column, right-click the address and select 'disassemble this memory region'. In memory viewer (top window) you should see the AOB for that particular instruction location.
|
|
| Back to top |
|
 |
|